Continuous Authentication (4)
BLOG LISTINGS
October 9, 2024
Contact centers play a huge role in customer satisfaction and are essential to operations for large consumer-facing...
October 2, 2024
BPO contact centers handle sensitive customer information daily, making them prime targets for attackers. Instead of...
September 26, 2024
Introduction In a recent security horror story, KnowBe4, a renowned security awareness training company, hired a...
September 10, 2024
Business Process Outsourcing (BPO) security professionals face many challenges in safeguarding their organizations....
September 5, 2024
BPOs need help with data security: faced with a mountain of challenges, they must secure their operations without...
August 16, 2024
Clean desk policies are so standard in BPO contact centers that they are often considered a requirement–although...
Posts by Tag
- 2FA (8)
- Agent Identity (4)
- Agile (1)
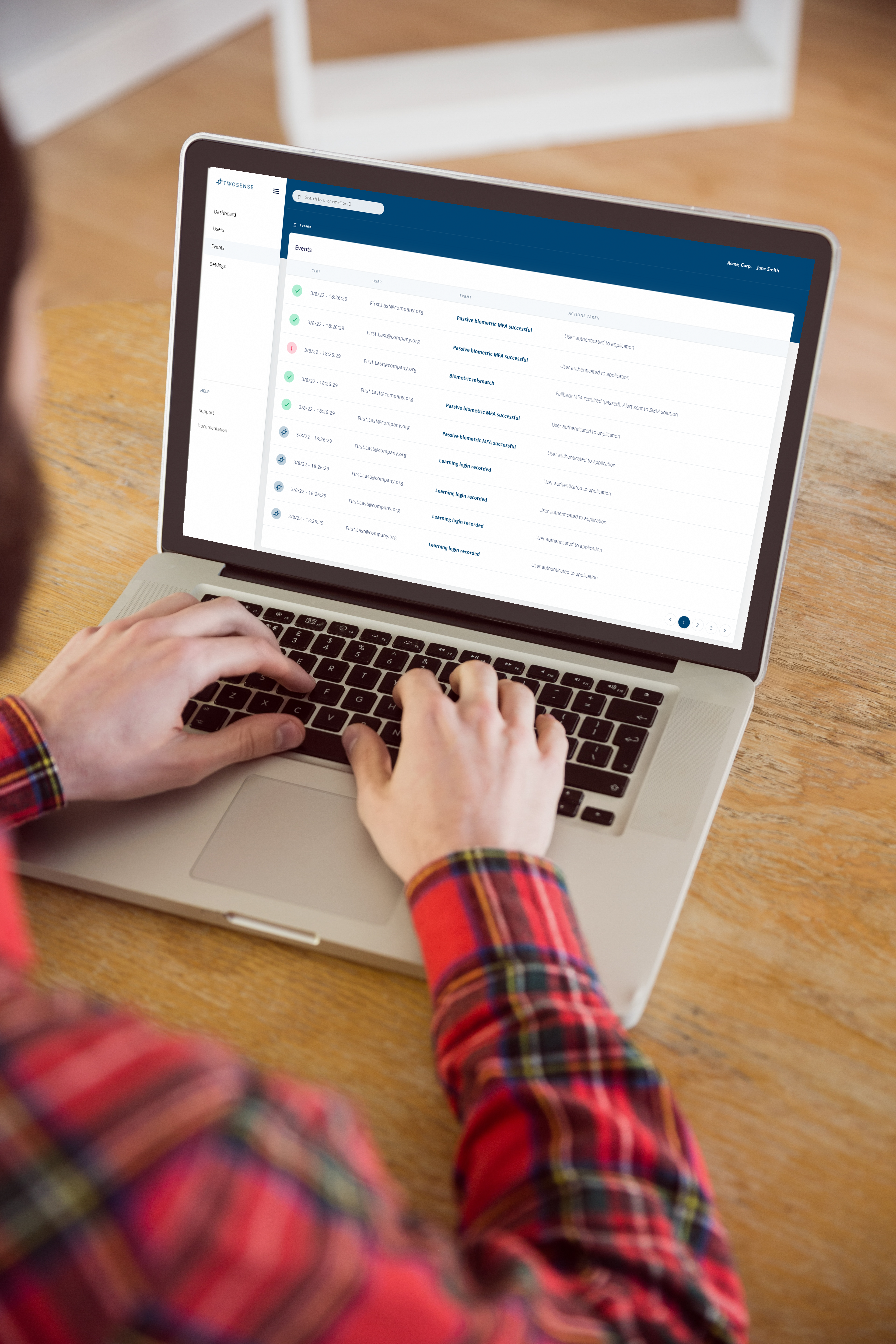
- Automated MFA (5)
- Behavioral Authentication (2)
- Behavioral MFA (27)
- Biometrics (19)
- BPO (22)
- Burnout (1)
- CCaaS (1)
- Clean Desk MFA (1)
- Compensating Controls (2)
- Compliance (18)
- Contact Centers (49)
- Continuous Authentication (63)
- Continuous MFA (25)
- Cryptocurrency (1)
- Culture (3)
- Cyber Insurance (1)
- Cybersecurity (27)
- Data Breach (12)
- Data Science (1)
- Deep Work (1)
- Flow State (1)
- Hard Tokens (1)
- Identity Access Management (1)
- Infosec (14)
- Machine Learning (5)
- Mental Health (3)
- MFA (5)
- Multi-Factor Authentication (47)
- Passive Biometrics (10)
- Passive MFA (1)
- Password Sharing (1)
- Passwordless (1)
- PCI Compliance (18)
- PCI DSS (14)
- Phishing (5)
- Phishing-Resistant MFA (10)
- Preparedness (1)
- Prompt Bombing (3)
- RFPs (1)
- SOC2 (1)
- Social Engineering (4)
- Software MFA (1)
- Twosense Team (2)
- Unauthorized Users (1)
- Unphishable MFA (11)
- WAHA (1)
- Webinar (1)
- WFH (4)
- Zero Trust (10)
Recent Posts
Sign Up for our Blog
We will never share your email address with third parties.